Every time a driver parks a 2024 Tesla Model 3 or a Cybertruck, they are leaving behind a sophisticated digital entity that continues to pulse with data long after the garage door has closed. This reality represents a fundamental shift in the relationship between man and machine, where the vehicle is no longer a passive tool but an active participant in a global network. Research from Northeastern University’s Khoury College of Computer Science recently demonstrated that this “always-on” state is not merely a convenience for software updates; it is a persistent invitation for digital intrusion that users are currently powerless to decline. Unlike the handheld electronics that define modern life, these vehicles lack an accessible “airplane mode” or a way to purge data-hungry background processes, leaving owners in a state of perpetual, unmonitored connectivity.
The significance of these findings extends far beyond the sleek glass and steel of a high-end electric vehicle. As the automotive industry moves toward a future defined by software rather than internal combustion, the car has become a primary target for sophisticated cyberattacks. This research, conducted by experts such as Professor Aanjhan Ranganathan and a dedicated team of doctoral researchers, underscores a critical gap in consumer rights and safety. While a smartphone user can choose to uninstall a suspicious app or disable location services, a Tesla owner inherits a closed ecosystem where the networking hardware remains active and invisible. The result is a vehicle that remains vulnerable to tracking and interception from the moment it leaves the assembly line until it reaches the end of its operational life.
The “Computer on Wheels” That Never Truly Sleeps
The modern driving experience is increasingly defined by a hidden heartbeat of digital signals that maintain a car’s readiness for remote commands and over-the-air improvements. For owners of the 2024 Tesla Model 3 and the Cybertruck, the car acts as a high-performance networked device that essentially functions as a server on four wheels. This persistent digital presence is necessary for features like Sentry Mode, remote climate control, and real-time navigation updates, yet it also means the vehicle is never truly “off.” The research revealed that this constant state of alertness creates a double-edged sword; while the car is always ready to serve the owner, it is also always ready to listen to potential intruders who know how to speak its digital language.
Furthermore, the lack of transparency regarding these background operations leaves the average consumer in the dark about how much data their vehicle is broadcasting into the atmosphere. Most drivers would be surprised to learn that their vehicle maintains an active link to cellular towers even when locked in a secure parking structure. This architectural choice removes the traditional “air gap” that once protected automotive control systems from the outside world. Without the ability for an owner to monitor these connections or toggle them off, the car becomes a black box of communication, operating under a set of rules established by the manufacturer and the cellular provider rather than the person behind the wheel.
Why Persistent Connectivity Is the New Automotive Frontier
The transition from traditional mechanical engineering to software-defined mobility has effectively shifted the primary attack surface of the vehicle from the physical to the ethereal. Modern cars rely on a dense web of technologies including 4G LTE, Wi-Fi, GPS, and Vehicle-to-Everything (V2X) protocols to facilitate the constant flow of information required for smart-city integration. This connectivity is marketed as a peak convenience, allowing for seamless navigation and safety diagnostics that can prevent a breakdown before it happens. However, this same convenience provides a window of opportunity for sophisticated actors to intercept data or disrupt essential communications without ever needing physical access to the car.
As vehicles become more integrated into the broader smart city infrastructure, the security of these wireless links moves from a matter of individual privacy to a significant concern for public safety. A compromised vehicle in a high-density urban environment could theoretically be used to relay false information to traffic management systems or other connected cars. The research suggests that the current focus on feature-rich connectivity has outpaced the development of defensive measures. This creates a landscape where the car’s constant state of readiness is its greatest vulnerability, as it remains perpetually engaged with a network that is not always under the control of the manufacturer or the user.
Inside the Vulnerabilities: Tracking and Communication Exploits
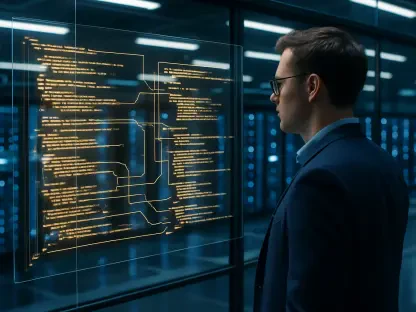
The research from Northeastern University detailed how attackers can exploit the foundational protocols of cellular networking to compromise a vehicle’s integrity through remote means. One of the most alarming methods involves the use of “fake cell towers” or rogue base stations to capture a vehicle’s International Mobile Subscriber Identity (IMSI). Every Tesla equipped with a cellular modem carries this unique identifier, which is typically used for network authentication. By tricking the car into a digital handshake, an attacker can obtain this permanent ID and use it to track the vehicle’s movements with pinpoint accuracy across different locations. This bypasses the privacy protections that cellular carriers usually implement to hide a user’s location through temporary identities.
Beyond simple tracking, these rogue towers allow an attacker to position themselves as a “man-in-the-middle” between the car and Tesla’s backend servers. In this position, the intruder can intercept sensitive data traffic or force the vehicle’s modem to “fall back” to insecure, legacy 2G or 3G networking modes. These older standards were developed long before modern encryption techniques were standardized, making it significantly easier for hackers to crack the communication stacks and view the data being transmitted. This type of exploit demonstrates that even the most advanced vehicle is only as secure as the weakest link in the cellular network it chooses to trust at any given moment.
The study also identified significant risks within the messaging and emergency alert systems that are built into these cellular modems. These engineering-level channels, such as SMS protocols, can be abused to flood the driver’s interface with unauthorized spam or issue spoofed emergency alerts designed to cause panic. In more severe cases, an attacker could initiate a Denial of Service (DoS) attack, effectively clogging the vehicle’s communication pipeline. This would block legitimate, safety-critical data transfers, such as emergency braking notifications or road hazard warnings from other vehicles, potentially leading to dangerous situations on the road where the driver is unaware that their safety systems have been silenced.
A Systemic Crisis in the Automotive Supply Chain
While the study utilized the 2024 Tesla Model 3 and Cybertruck as its primary subjects, the vulnerabilities discovered are not isolated to a single brand but are endemic to the entire automotive supply chain. The root of the problem lies in the third-party hardware that handles the vehicle’s connectivity—specifically the cellular modems manufactured by global giants like Qualcomm and Quectel. Because these specific modem chips are industry standards used by millions of vehicles from a variety of manufacturers, a flaw identified in one “stack” of software creates a ripple effect across the entire global transportation sector. This means that the security risks found in a Tesla are likely mirrored in luxury sedans and family SUVs from completely different companies.
This reliance on a handful of global suppliers creates a centralized point of failure that makes the industry vulnerable to widespread exploitation. Furthermore, the “black box” nature of these components makes independent security auditing an uphill battle for researchers. Uncovering these flaws required a rare and expensive collaboration between academic researchers and advocates from Consumer Reports to even gain access to the vehicles and the necessary testing equipment. This highlights a concerning lack of transparency in the industry, where manufacturers often hide behind proprietary hardware designs, preventing independent safety advocates from identifying and patching risks before they can be exploited by malicious actors in the wild.
Strategies for a More Secure Connected Future
To navigate toward a more secure automotive landscape, the industry must prioritize the hardening of foundational links over the addition of new digital features. One of the most effective steps identified was the aggressive transition toward 5G networking. Unlike the older LTE standards, 5G offers superior identity protection that makes IMSI catching and unauthorized tracking significantly more difficult to execute. Simultaneously, manufacturers must take the decisive step of disabling the ability for modems to “fall back” to 2G or 3G networks. By closing this door, automakers can effectively eliminate the primary gateway used by hackers to bypass modern encryption and gain a foothold in the vehicle’s communication system.
The path forward also demanded a fundamental shift in how hardware and software are vetted across the global supply chain. It was concluded that automakers must align with international cybersecurity standards, such as those established by the ISO and the United Nations, to create a baseline of security for all connected components. Greater collaboration between car brands and modem suppliers was viewed as essential to ensure that the code running on wireless chips is as rigorously tested as the vehicle’s own driving software. Ultimately, these measures sought to restore a level of control to the consumer, ensuring that the “always-on” nature of the modern car does not come at the expense of the owner’s privacy or safety.