

A striking paradox defined India's smartphone landscape in 2025, where the sheer number of devices sold barely moved the needle, yet the market's overall value surged, painting a clear picture of a nation trading up. The narrative is no longer one of volume at all costs but of a strategic and
A revolutionary breakthrough in quantum computing thermal management has demonstrated a novel method where engineered noise, traditionally considered a primary source of computational error and decoherence, is harnessed as a powerful and efficient refrigeration tool. This development represents a

A widely followed on-chain metric might be painting an incomplete picture of Bitcoin's market health, potentially lulling traders into a false sense of security while significant selling pressure builds beneath the surface. A detailed analysis reveals a critical discrepancy in how the activity of

For years, the rapid advancement of artificial intelligence has disproportionately favored widely spoken languages, leaving the rich linguistic diversity of smaller regions like the Baltic States underserved by cutting-edge natural language processing tools. Addressing this technological gap,

The digital battlefields of today are not being defined by sentient artificial intelligences locked in an autonomous war, but by the strategic and pragmatic race to build the most effective human-machine teams. This new era of cybersecurity has shifted the focus from speculative conflicts to the

In an era where digital systems are the backbone of modern psychotherapy, the responsibility to protect deeply personal client data has never been more critical. We're joined by Oscar Vail, a technology expert whose work at the forefront of emerging fields like quantum computing and robotics gives
A multi-million-dollar system modernization, meticulously designed to secure government data for the next decade, could become obsolete before it is even fully deployed. This is not a hypothetical scenario; it is the critical oversight that one of the nation's top cybersecurity officials warns is

Confronting the growing complexities of long-term financial planning, from saving for a child's future to investing for retirement, often transforms the abstract concept of money into a tangible source of daily stress. The world of personal finance management represents a significant advancement in
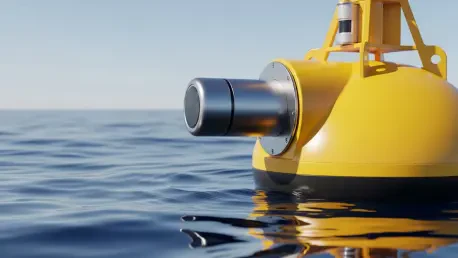
The boundless energy potential contained within the ocean's natural temperature variations is now being unlocked by a technology that cleverly merges 19th-century physics with 21st-century material science and engineering. The technology of marine thermomagnetic generators represents a significant
A sheet of material thinner than a human hair folds itself into a walking robot, twists like a corkscrew, and flips over, all without a single motor or wire attached. This is not science fiction but the reality emerging from research at McGill University, where engineers have developed a new class
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy