The rapid expansion of high-speed satellite connectivity across the global merchant fleet has inadvertently created a sprawling digital ecosystem where the primary vulnerability is no longer the software code itself but the individuals who possess the keys to the kingdom. Modern maritime operations now rely on a continuous stream of data for fuel optimization and remote monitoring, yet this connectivity has expanded the attack surface beyond traditional defenses. Recent intelligence indicates a startling shift where approximately sixty-nine percent of observed risks now originate from compromised user credentials, whereas software exploits account for a mere twelve percent. This evolution suggests that malicious actors are no longer wasting time hammering at reinforced digital gates; instead, they are simply logging in using stolen or poorly managed access rights. This change in tactics reflects a broader trend where the human element serves as the gateway for sophisticated breaches that bypass standard encryption.
Bridging the Gap: Operational and Information Technology
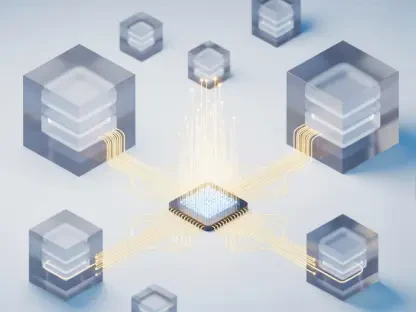
The integration of information technology with vessel operational technology has introduced a level of complexity that frequently outpaces current security protocols. In the current landscape of 2026, over sixty percent of assessed maritime sites utilize shared infrastructure, which often masks deep-seated vulnerabilities within the machinery. Furthermore, more than seventy percent of these sites possess undocumented or unsecured connections that provide silent pathways into the heart of a ship’s navigation and propulsion systems. These unmanaged assets create significant blind spots, allowing sophisticated attackers to move laterally through the internal network with minimal risk of detection once an initial entry point is secured. The lack of distinct segmentation between crew entertainment systems and critical ship management tools further exacerbates the problem. Without a clear inventory of every connected device, fleet managers remain largely unaware of how many potential backdoors exist.
Strategies for Resilience: Enhancing Human-Centric Security
The pervasive nature of social engineering became the primary driver for maritime security alerts, with eighty-two percent of incidents occurring within crew network zones. Phishing campaigns remained remarkably effective, as twenty percent of users interacted with malicious links that harvested sensitive credentials. In response to the surge in ransomware incidents, which grew to nearly eight thousand cases annually, the industry moved toward an identity-first security model. This transition required shipowners to implement stricter controls over trusted access and conduct comprehensive mapping of all network connections to eliminate hidden entry points. Operators integrated multi-factor authentication and behavioral monitoring directly into the operational infrastructure to detect anomalies in real time. Ultimately, the industry shifted its focus from merely purchasing new digital tools to the rigorous management of the personnel and credentials that operated them. This proactive stance ensured that cyber resilience was woven into the fabric of daily vessel management.