
A seemingly innocuous flaw in a widely used open-source cryptographic library managed to silently undermine the security of hundreds of thousands of websites, demonstrating that the lock icon in a browser's address bar was not the impenetrable shield many believed it to be. Discovered in 2014, the

The rapidly expanding commercial space industry presents a landscape of immense opportunity and equally significant peril, with private investors often hesitant to commit capital to the high-risk, high-reward field of space cybersecurity. This reluctance creates a dangerous innovation vacuum,

As the world pivots toward clean energy, the safe handling of hydrogen is paramount. Oscar Vail, a technology expert with a deep focus on the innovations shaping our future, joins us to discuss a groundbreaking new sensor poised to solve one of the biggest challenges in hydrogen safety: humidity.
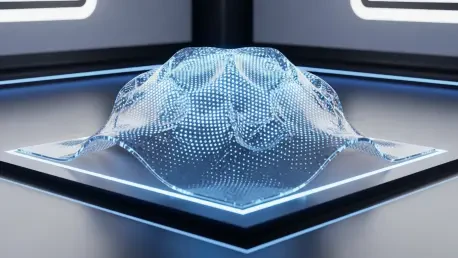
A significant breakthrough in materials science has been achieved by researchers at Penn State, who have successfully engineered a programmable "smart synthetic skin" with the remarkable ability to dynamically alter its appearance, texture, and physical shape on command. This innovative

The long-standing dilemma of Bitcoin's scalability, which often resulted in slow transaction times and high fees during periods of network congestion, has historically limited its potential as a daily medium of exchange. Recent technological breakthroughs are now directly addressing these

A bombshell lawsuit filed in early 2026 has sent shockwaves through the digital privacy community, alleging that Meta possesses a secret capability to read the supposedly private messages of its two billion WhatsApp users. The claims, amplified by influential online personalities, paint a grim