
Modern digital enterprises are currently facing an unprecedented explosion of cloud-native complexity that traditional security architectures struggle to monitor effectively. As organizations deploy thousands of microservices across hybrid environments, the distance between security intelligence
The landscape of modern conflict has shifted toward the digital exploitation of civilian infrastructure, where Internet Protocol (IP) cameras are no longer just tools for safety but active assets for foreign intelligence. Recent high-profile operations, such as the compromise of Tehran’s traffic

The fundamental trust placed in high-stakes academic evaluations depends entirely on the robust security of the underlying digital infrastructure, a reality that is currently being tested as the National Testing Agency faces mounting criticism over its NEET UG 2026 re-examination portal. As

Oscar Vail stands at the cutting edge of modern technology, where his expertise in quantum computing and robotics gives him a unique vantage point on the shifting sands of digital security. With a career deeply rooted in open-source projects, he understands the delicate balance between system

The promise of high-throughput blockchain architecture often collides with the harsh reality of software complexity, as seen during the recent series of disruptions that paralyzed the Sui Network. Developed by veterans of Meta’s Diem project, the network was marketed as a next-generation solution

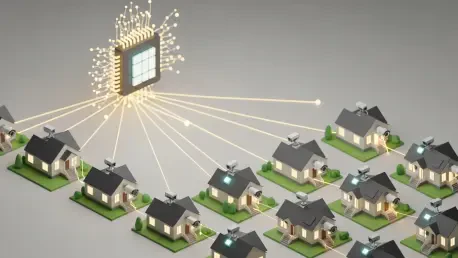
The rapid proliferation of large language models across professional environments has created a landscape where artificial intelligence acts as both a revolutionary productivity enhancer and a complex primary vector for sophisticated cyberattacks. While these tools have drastically improved the
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24