
The digital landscape of Latin America faced an unprecedented crisis between late 2025 and early 2026 as autonomous AI agents bypassed traditional cybersecurity defenses to execute a massive breach of Mexican government infrastructure. This incident represents a pivotal moment in the evolution of

The staggering volume of capital currently locked within decentralized protocols has transformed the pursuit of smart contract security from a niche technical concern into a cornerstone of global financial stability. As we navigate the complexities of 2026, the Open Worldwide Application Security

As the digital frontier expands, the promise of artificial intelligence has often been framed as a great equalizer, a tool capable of providing the sum of human knowledge to anyone with an internet connection. However, recent findings from the MIT Center for Constructive Communication suggest a

As a technology expert with a deep-seated interest in the frontier fields of quantum computing, robotics, and open-source projects, I've watched AI's integration into cybersecurity with immense fascination. Today, we're going to pull back the curtain on how artificial intelligence is not just an

Data privacy is rapidly approaching a fundamental transformation, poised to shift from a specialized, often complex, corporate concern into an unremarkable yet essential component of daily business operations. This evolution signifies privacy’s maturation into a non-negotiable, foundational
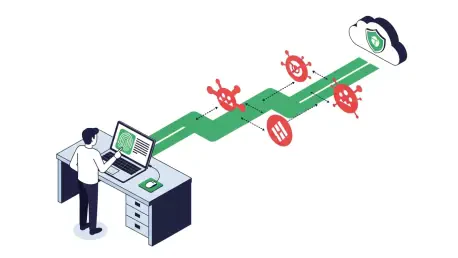
In the relentless cat-and-mouse game of cybersecurity, the ground beneath our feet is shifting. For years, Multi-Factor Authentication (MFA) has been the bedrock of digital defense, a trusted shield against a barrage of credential-based attacks. But as attackers evolve, powered by sophisticated