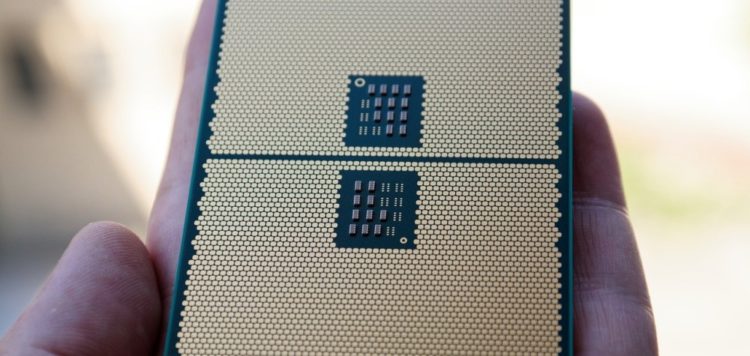
Last year, we reported on a vulnerability that could allow an attacker to bypass the protections afforded by AMD’s secure encrypted virtualization (SEV) technology, found in its EPYC server processors.
When the issue came to light, AMD dismissed the exploit on the grounds that it requires physical access to the hardware, but this is only half the story. The researcher responsible for the original discovery, Robert Buhren, says physical access is only required in the first instance, after which the bug could be exploited remotely to disastrous effect.