The recent emergence of the Mirax Android Remote Access Trojan signifies a sophisticated shift in the cybercrime landscape where mobile devices are no longer just targets for direct financial theft but are increasingly integrated into complex botnet infrastructures. Discovered by security researchers during the first quarter of 2026, this malware distinguishes itself from the common Malware-as-a-Service model by operating within a strictly vetted circle of Russian-speaking affiliates. This exclusivity suggests a deliberate strategy to maintain operational longevity and minimize the risk of early detection by global security agencies. By focusing on a closed ecosystem, the developers of Mirax ensure that their tactics remain effective for longer periods compared to widely distributed malware families. The primary objective appears to be the dual exploitation of compromised hardware, turning everyday smartphones into both sources of stolen banking credentials and nodes within a global residential proxy network. This approach reflects a maturing threat environment where attackers prioritize versatility and stealth over the sheer volume of infections, marking a significant evolution in how mobile devices are weaponized in 2026.
Strategic Distribution and Multi-Stage Infection
The Mechanism of Deception and Delivery
Cybercriminals behind the Mirax campaign have successfully exploited the trust associated with major social media platforms by utilizing deceptive Meta advertisements on Facebook and Instagram to ensnare victims. These advertisements typically promote fraudulent IPTV applications designed for sports streaming, a lure that has proven particularly effective in regions like Spain where demand for such services is high. When a user interacts with these ads, they are redirected to a malicious landing page that performs sophisticated environmental checks to ensure only genuine mobile browsers can access the final payload. By analyzing HTTP headers, the landing page effectively filters out automated security scanners and web crawlers that would otherwise flag the malicious intent. Once the environment is confirmed as a legitimate target, the infection chain initiates a multi-stage process involving complex packing techniques. The malware utilizes GoldCrypt and RC4 decryption methods to unpack its final APK file, ensuring that the malicious code remains hidden from static analysis tools until the very last moment of execution on the device.
This deceptive delivery method highlights the increasing difficulty in distinguishing between legitimate software and sophisticated mobile threats in the modern digital marketplace. Once the user is tricked into installing the malicious APK, the malware immediately begins its efforts to secure a permanent foothold on the operating system. The transition from a seemingly harmless sports streaming application to a fully functional remote access tool happens almost instantaneously, leaving the user unaware of the underlying compromise. The developers have meticulously engineered this initial phase to bypass traditional perimeter defenses, relying on the user’s own actions to authorize the installation of the software. This reliance on social engineering, combined with technical evasion techniques, creates a potent delivery mechanism that is difficult to neutralize without comprehensive user education and advanced behavioral detection systems. As the infection progresses, the malware shifts its focus from remaining undetected during delivery to gaining the deep system permissions required for its more intrusive activities, setting the stage for total device control.
Deep System Integration and Credential Harvesting
Upon gaining entry to the device, Mirax leverages Android’s Accessibility Services to obtain deep system permissions, a critical step that allows the malware to bypass many built-in security features. By convincing the user to enable these services under the guise of application functionality, the Trojan gains the ability to observe user interactions and manipulate the interface of other installed apps. This capability is central to its banking theft functions, as it allows the malware to present fake HTML overlays when a user attempts to open a legitimate financial application. Mirax is currently programmed to target 182 specific applications, including banking tools and cryptocurrency wallets, harvesting credentials in real-time as users enter them. This UI automation allows the attackers to intercept sensitive information before it can be encrypted or protected by the application’s own security measures. Furthermore, the malware includes a Virtual Network Computing capability, which provides attackers with direct remote control over the infected device to perform unauthorized transactions manually.
The sophistication of these harvesting techniques is matched by the malware’s ability to maintain persistence and evade manual removal by the user. By integrating itself into the core functions of the device, Mirax can intercept system notifications and block attempts to access security settings that might lead to its uninstallation. The use of Accessibility Services also enables the malware to click buttons or grant itself further permissions without any direct user intervention, effectively creating an automated environment for data exfiltration. This level of control ensures that once a device is compromised, the attackers have a reliable stream of high-value data including login credentials, two-factor authentication codes, and personal identification information. The ability to switch between automated credential harvesting and manual remote control makes Mirax a particularly dangerous threat to mobile banking users. This dual approach allows the threat actors to adapt their tactics based on the specific security measures of the targeted financial institution, ensuring a high success rate for their fraudulent activities while maximizing the illicit gains from each individual infection.
The Transformation into a Residential Proxy Network
Technical Architecture of the SOCKS5 Botnet
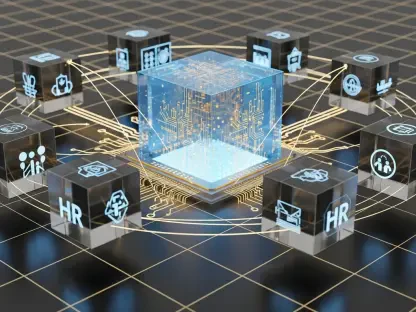
What truly separates Mirax from traditional banking Trojans is its integrated SOCKS5 proxy capability, which recruits infected devices into a vast residential proxy network. This transformation is achieved through the use of Yamux multiplexing over WebSockets, allowing the malware to establish stable and versatile communication channels between the device and the attacker’s infrastructure. By routing malicious traffic through the legitimate IP addresses of everyday users, the attackers can perform a variety of illicit activities, such as Distributed Denial of Service attacks or credential stuffing, with a significantly lower risk of being blocked by IP reputation systems. This commodification of the infected device’s internet connection creates a secondary revenue stream for the botnet operators, who can sell access to these residential proxies on the dark web. The use of WebSockets ensures that the connection remains bidirectional and persistent, allowing the command-and-control server to push new instructions or data exfiltration commands to the device at any time, even if it is behind a firewall or a carrier-grade NAT.
The infrastructure supporting this proxy network is equally robust, employing a gate server architecture to hide the true location of the primary command-and-control servers. This layered approach ensures that even if a single proxy node or gate server is discovered and taken down, the central management of the botnet remains intact and hidden from investigators. The multiplexing capabilities of Yamux allow for multiple data streams to be handled simultaneously over a single connection, maximizing the efficiency of the proxy service without causing noticeable performance degradation on the host device. This stealthy operation is crucial for maintaining the longevity of the botnet, as users are unlikely to notice that their smartphone is being used as a relay for international cyberattacks. By turning mobile devices into decentralized proxy nodes, the Mirax operators have created a resilient and highly scalable infrastructure that challenges traditional methods of network-based threat detection and mitigation. This evolution marks a dangerous trend where mobile malware is no longer just a tool for theft but a fundamental component of broader cybercrime infrastructure.
Mitigating the Rise of Hybrid Mobile Threats
The discovery of Mirax prompted a reevaluation of mobile security strategies, emphasizing the need for more proactive measures against hybrid threats that combine data theft with botnet capabilities. Security researchers recommended that users remain extremely cautious when interacting with advertisements on social media, especially those promoting third-party applications that are not available through official app stores. It was observed that maintaining strict control over Accessibility Services and regularly auditing the permissions granted to installed apps served as an effective defense against the most intrusive functions of the malware. Organizations were advised to implement advanced mobile threat defense solutions that could detect the subtle behavioral anomalies associated with SOCKS5 proxy activity and unauthorized UI overlays. Furthermore, financial institutions were encouraged to adopt stronger multi-factor authentication methods that did not rely solely on SMS or on-device notifications, which could be easily intercepted by sophisticated Trojans like Mirax.
The collaborative effort between cybersecurity firms and platform providers became essential in dismantling the infrastructure used by the Mirax affiliates. By sharing threat intelligence and identifying the specific patterns used in the deceptive Meta ads, the industry worked toward a more unified response to this evolving threat landscape. The focus shifted toward identifying the gate servers and command-and-control nodes, disrupting the communication channels that allowed the botnet to function effectively. For individual users, the primary takeaway was the importance of device hygiene and the avoidance of high-risk behaviors, such as sideloading applications from unverified sources. As mobile devices continued to be a central part of daily life, the lessons learned from the Mirax campaign highlighted the ongoing necessity for vigilance and the continuous update of security protocols. The research community concluded that the integration of proxy capabilities into traditional banking malware represented a permanent shift in attacker methodology, requiring a corresponding evolution in the tools and techniques used to protect global mobile ecosystems.