The digital fortress that has shielded hundreds of billions of dollars in decentralized wealth for nearly two decades is now facing a mathematical siege that could redefine the future of global finance. For years, Bitcoin has been considered virtually unhackable, relying on cryptographic principles that would require millions of years for any existing supercomputer to decipher through brute force. However, as of 2026, a recent analysis by Project Eleven suggests that this period of perceived invulnerability is rapidly coming to an end due to the maturation of quantum computing technologies. The report highlights that the mathematical foundations of the network are approaching a potential obsolescence point where the “unforgeable scarcity” of the asset could be compromised. If the ecosystem fails to adapt to these shifts, machines capable of performing calculations in seconds that were once deemed impossible could dismantle the integrity of the ledger, turning a global store of value into a vulnerable target for state actors and sophisticated hackers alike.
Understanding the Vulnerability of Cryptographic Foundations
The primary technical concern centers on the Elliptic Curve Digital Signature Algorithm, which serves as the cryptographic gatekeeper for every transaction on the network. While classical computers operate on binary bits, quantum machines utilize qubits, which allow them to exist in multiple states simultaneously and perform parallel computations at an exponential scale. If a quantum processor achieves sufficient coherence to run Shor’s algorithm effectively, it could derive a private key from a publicly available key almost instantaneously. This capability effectively breaks the fundamental lock on the world’s most famous digital vault, as any observer of the blockchain could potentially calculate the spending credentials for any address they can see. This isn’t merely a theoretical problem for the distant future; the rapid development of quantum error correction indicates that the threshold for a cryptographically relevant quantum computer is moving closer to reality, threatening the core security assumptions that have held firm since the network’s inception.
The timeline for these advancements is accelerating as massive investments pour into both private and state-sponsored quantum laboratories across the globe. Experts suggest that the window for the community to implement a robust defense is narrowing as the technology moves from the realm of academic research into practical, scalable application. While current quantum machines are not yet capable of executing a full-scale attack on the ledger, the pace of innovation suggests that a critical point could be reached between 2026 and 2031. This timeline leaves the ecosystem with very little room for error or delay in overhauling its cryptographic infrastructure. The threat is not static, and the transition to a post-quantum world requires a proactive shift before the first capable machine is switched on. Waiting for a successful exploit to occur would be catastrophic, as the mathematical walls protecting the network’s multi-billion dollar market capitalization would have already been breached beyond the point of any possible recovery.
The Massive Hurdle of Decentralized Governance
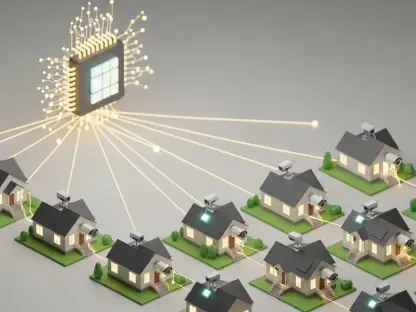
One of the most significant obstacles to securing the network against these emerging threats is the inherent lack of a central authority within the decentralized ecosystem. Unlike a traditional financial institution or a corporate entity, there is no chief executive officer to mandate an emergency security patch or force a synchronized software update across the globe. Implementing quantum-resistant cryptography requires a massive, coordinated effort from a diverse group of stakeholders, including independent developers, mining pools, and thousands of individual node operators. This decentralized nature is a primary strength against censorship and single points of failure, yet it makes rapid technological pivots notoriously difficult and prone to prolonged political infighting. History has shown that even minor changes to the protocol can lead to contentious debates and community fractures, suggesting that a fundamental cryptographic overhaul will face significant administrative and social hurdles before any technical implementation can actually take place on the main chain.
Furthermore, the vulnerability is not uniform across all addresses, as a significant portion of the total supply is stored in older formats where public keys are already visible on the ledger. These legacy addresses, which include millions of coins from the earliest days of the network, are particularly at risk because their public keys were revealed during the transaction process or are inherent in the address type. Unlike modern addresses that hash the public key for added protection, these “p2pkh” scripts are transparent to a quantum observer. Because many of these coins are held in lost wallets or by inactive users, they cannot be moved to new, secure standards through a standard software update. This creates a multi-billion dollar bounty that would be ripe for the taking by whoever develops the first functional quantum computer. This scenario presents a moral and technical dilemmthe community may have to decide whether to allow these funds to be stolen or to implement a controversial plan that could effectively burn or lock addresses that fail to migrate in time.
Balancing the Timeline for Global Migration
The strategic dilemma facing the community involves finding a balance between the urgency of the threat and the stability of the protocol. Moving too slowly results in a catastrophic loss of funds and a total collapse of global trust, yet rushing to adopt experimental algorithms could be equally damaging. Many proposed quantum-resistant signatures, such as those based on lattice-based cryptography, are significantly larger than current signatures, which could lead to network congestion and higher transaction fees. Integrating these unproven standards too early might introduce unforeseen bugs or make the network so inefficient that it loses its competitive advantage as a streamlined medium of exchange. The process of vetting these new mathematical frameworks is a high-stakes balancing act that will define the next phase of the network’s existence. Developers must ensure that the chosen solution is not only secure against quantum attacks but also compatible with the existing infrastructure to avoid a permanent split in the network that could dilute the value and security of the entire ecosystem.
To ensure long-term survival, the community prioritized the development of hybrid cryptographic standards that allowed for a gradual transition while the existing walls were still standing. Stakeholders recognized that the most effective solution involved the creation of new address types that utilized post-quantum signatures, alongside clear education for users on the necessity of manual migration. Proactive measures were taken to incentivize the movement of funds from vulnerable legacy scripts to quantum-secure vaults well before the projected 2031 deadline. The focus shifted toward standardized testing of lattice-based and hash-based signature schemes to ensure that the network’s efficiency remained intact during the transition. Ultimately, the survival of the ledger depended on the collective willingness to embrace change before the threat became a reality. By establishing a clear technical roadmap and fostering global cooperation, the ecosystem demonstrated that its decentralized governance could adapt to existential challenges, ensuring that the store of value remained secure for the next generation of users.