The sudden paralysis of digital learning platforms during the critical final exam window of the academic calendar has exposed a fragile infrastructure that millions of students rely upon for their daily education and professional advancement. When Instructure’s Canvas learning management system experienced two major security breaches within a single week, the ripple effects were felt across the entire American educational landscape. These incidents did not merely represent a technical glitch but highlighted a fundamental shift in the risk profile of modern classrooms where student data is increasingly digitized. As schools and universities pushed toward a paperless environment, the centralization of student records, assignments, and personal communications created a lucrative target for international cybercriminal syndicates. The fallout from these unauthorized access events forced a national conversation regarding the trade-offs between convenience and security, revealing that the digital tools meant to empower educators can simultaneously become their greatest operational liability when defenses are breached.
The Anatomy of the Breach and Systemic Vulnerabilities
Exploit Mechanics: The Free-For-Teacher Flaw
The technical origin of the crisis was traced back to a specific vulnerability within the platform’s “Free-For-Teacher” account system, which provides a gateway for independent educators. Investigation into the timeline revealed that an initial unauthorized entry occurred on April 29, followed by a more aggressive intrusion that was detected on May 7. This secondary attack was particularly sophisticated, as the threat actors leveraged the existing infrastructure to bypass standard security protocols that are typically robust for large institutional contracts. By exploiting this secondary access point, the hackers were able to move laterally within the environment, gaining the ability to inject custom content into user interfaces. This prompted Instructure to take the unprecedented step of temporarily disabling all free-tier accounts to isolate the threat and conduct a deep-dive forensic audit of the underlying source code. This mitigation strategy, while necessary for long-term security, immediately severed access for thousands of legitimate users during their most stressful academic period.
Building on this technical discovery, the incident underscored a significant architectural risk inherent in providing various tiers of service within a shared ecosystem. While institutional portals were thought to be isolated, the shared codebase allowed the vulnerabilities in the teacher-facing side to impact the broader user experience. Security professionals noted that this “entry-point asymmetry” is a common tactic where attackers find the weakest link in a complex software-as-a-service model to gain a foothold. The ability of the intruders to remain undetected for several days after the initial April breach indicated a level of persistence and stealth that is characteristic of high-level cybercriminal organizations. Furthermore, the decision to shut down parts of the platform showcased the extreme measures required to remediate flaws in real-time when the integrity of a national learning system is at stake. This reactive approach highlighted the need for more rigorous pre-deployment testing of peripheral features that might inadvertently serve as backdoors into critical core data environments.
Immediate Academic Fallout: Institutional Responses
The timing of the May 7 incident coincided perfectly with year-end assessments, resulting in immediate operational paralysis for some of the most prestigious academic institutions. Pennsylvania State University took a definitive stance by canceling all scheduled tests for the evening of the breach and the entire following day, recognizing that the lack of system reliability compromised the fairness of the exams. Other schools, including Harvard University and the University of Pennsylvania, reported that students were greeted with unauthorized messages from a cybercrime group known as “ShinyHunters” rather than their expected course content. This visual takeover of the student portal was more than a nuisance; it created a sense of digital insecurity that distracted thousands of learners during a high-stakes week. Administrators were forced to improvise academic policies, granting broad extensions and grace periods for assignments that could not be submitted through the standard channels, which effectively disrupted the grading cycles and administrative timelines.
Moreover, the psychological and administrative toll on the education sector was exacerbated by the uncertainty surrounding the safety of personal information. Even after Instructure declared that the core systems were back online and secured, several cautious district administrators chose to keep their local portals disabled until their internal security teams could verify the situation. This lack of centralized trust demonstrated the fragility of the relationship between third-party ed-tech vendors and the public institutions that serve as their primary clients. Faculty members were forced to pivot back to manual methods of instruction or alternative communication platforms, highlighting how deeply dependent modern pedagogy has become on a single piece of software infrastructure. The disruption proved that when a primary learning management system fails, the entire educational workflow of a university can grind to a halt within minutes. The experience served as a jarring reminder that academic continuity is now inextricably linked to the uptime and security of cloud-based service providers.
Data Exposure and the Future of Digital Classrooms
Privacy Risks: Student Data as Leveraged Assets
The breaches resulted in the confirmed exposure of sensitive personal data, including full names, email addresses, and internal identification numbers that are unique to the educational environment. Even more concerning was the revelation that private messages exchanged between students and faculty were accessible to the intruders, providing a window into personal interactions and potentially confidential academic discussions. The group claiming responsibility, ShinyHunters, utilized this stolen data to create a public list of affected institutions, attempting to extort “settlements” from both the platform provider and individual schools. This transition from simple data theft to active extortion represents a dangerous evolution in how educational institutions are targeted, as student privacy is now used as a high-value bargaining chip. The permanent nature of digital theft means that once these records are exfiltrated, they can be utilized for identity theft or targeted phishing campaigns for years, creating a long-tail risk for every student whose data was caught in the cross-hairs.
This incident also brought significant attention to the systemic failures in federal oversight and the funding of cybersecurity initiatives for the education sector. Privacy advocates argued that the exposure of student messages was an invasive breach that should have been preventable with better encryption and data-handling practices. There is a growing concern that the rapid adoption of digital tools has outpaced the development of legal and ethical safeguards designed to protect minors and adult learners alike. The closure of key federal offices dedicated to educational technology and the subsequent reduction in cybersecurity grants left many school districts without the resources to properly audit their third-party vendors. Without standardized security requirements across the industry, schools often find themselves in a position where they must trust a provider’s marketing claims without the technical capacity to verify them. This power imbalance leaves users with little choice but to participate in a system that may not prioritize their privacy as much as their operational efficiency, creating a mandatory risk for anyone seeking a modern education.
Looking Forward: Reevaluating Technological Dependency
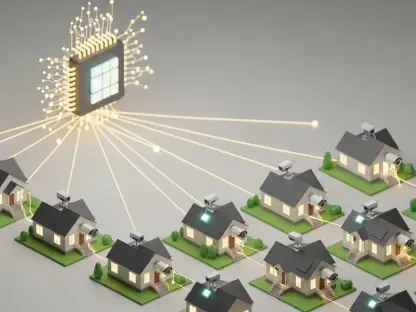
The events surrounding the May 2024 Canvas breach acted as a catalyst for a broader reevaluation of how technology is integrated into the daily operations of American schools. Many policy experts suggested that the incident proved the danger of a digital “monoculture,” where a single point of failure in one platform can disrupt the education of millions. Moving forward from 2026 to 2028, institutions must prioritize the development of offline contingencies and hybrid learning models that do not rely exclusively on a single cloud service for core functions. This shift requires a strategic investment in local data redundancy and the adoption of decentralized security protocols that can isolate breaches before they spread through a national network. Schools should also demand more transparency from their vendors, including regular third-party security audits and clear protocols for data breach notifications. By creating a more competitive and diverse ecosystem of educational tools, the sector can reduce the leverage that cybercriminals hold over these vital institutions and ensure that the digital classroom remains a safe environment for learning.
The resolution of the immediate threat in May 2024 provided several actionable insights that institutions implemented to bolster their long-term resilience. Administrators began to move away from all-in-one platforms in favor of modular systems that could be disconnected or replaced without collapsing the entire educational workflow. Technical teams focused on the implementation of multi-factor authentication for all users and the minimization of data retention, ensuring that if a breach did occur, the amount of sensitive information available to hackers was strictly limited. Policymakers at the state level also introduced new mandates for ed-tech security, requiring providers to adhere to strict encryption standards and to offer indemnity to schools affected by system failures. These proactive measures were designed to shift the burden of security back onto the vendors who profit from these services, creating a market incentive for higher safety standards. The crisis ultimately demonstrated that while technology remains an essential tool for progress, its benefits can only be realized if the underlying infrastructure is built on a foundation of rigorous security and institutional accountability.